Abstract
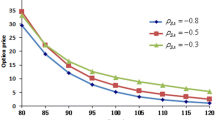
In this paper, we present a pricing model to value fade-in options with default risk, where the underlying asset price is driven by the Heston–Nandi GARCH process and is correlated with the intensity process. The explicit pricing formulae are obtained, which contain pricing formulae of vanilla European options with/without default risk as special cases. Finally, a comparative analysis of the impacts of default risk is provided.








Similar content being viewed by others
Notes
For simplicity, more parsimonious notations f(t), \(A_0(t)\), \(A_1(t)\), \(A_2(t)\), \(B_0(t)\), \(B_1(t)\) and \(B_2(t)\) are used here.
References
Alos, E., Antonelli, F., Ramponi, A., & Scarlatti, S. (2021). CVA and vulnerable options in stochastic volatility models. International Journal of Theoretical and Applied Finance, 24, 2150010.
Antonelli, F., Ramponi, A., & Scarlatti, S. (2021). CVA and vulnerable options pricing by correlation expansions. Annals of Operation Research, 299, 401–427.
Arora, N., Gandhi, P., & Longstaff, F. (2012). Counterparty credit risk and the credit default swap market. Journal of Financial Economics, 103, 280–293.
Bollerslev, T. (1986). Generalized autoregressive conditional heteroskedasticity. Journal of Econometrics, 81, 301–327.
Brigo, D., Capponi, A., & Pallavicini, A. (2014). Arbitrage-free bilateral counterparty risk valuation under collateralization and application to credit default swaps. Mathematical Finance, 24, 125–146.
Brigo, D., & Chourdakis, K. (2009). Counterparty risk for credit default swaps: Impact of spread volatility and default correlation. Journal of Theoretical and Applied Finance, 12, 1007–1026.
Brockhaus, O., Ferraris, A., Gallus, C., Long, D., Martin, R., & Overhaus, M. (1999). Modelling and hedging equity derivatives. Risk Books.
Christoffersen, P., Jacobs, K., Ornthanalai, C., & Wang, Y. (2008). Option valuation with long-run and short-run volatility components. Journal of Financial Economics, 90, 272–297.
Crépey, S. (2015a). Bilateral counterparty risk under funding constraints, part I: Pricing. Mathematical Finance, 25, 1–22.
Crépey, S. (2015b). Bilateral counterparty risk under funding constraints, part II: CVA. Mathematical Finance, 25, 23–50.
Duan, J., Gauthier, G., & Simonato, J. (1999). An analytical approximation for the GARCH option pricing model. Journal of Computational Finance, 2, 75–116.
Fard, F. (2015). Analytical pricing of vulnerable options under a generalized jump-diffusion model. Insurance: Mathematics and Economics, 60, 19–28.
Griebsch, S., & Wystup, U. (2011). On the valuation of fader and discrete barrier options in Heston’s stochastic volatility model. Quantitative Finance, 11, 693–709.
Heston, S., & Nandi, S. (2000). A closed-form GARCH option valuation model. Review of Financial Studies, 13, 585–625.
Johnson, H., & Stulz, R. (1987). The pricing of options with default risk. Journal of Finance, 42, 267–280.
Kendall, M., & Stuart, A. (1977). The advanced theory of statistics (Vol. 1). Macmillan.
Leung, S., & Kwok, Y. (2005). Credit default swap valuation with counterparty risk. The Kyoto Economic Review, 74, 25–45.
Li, G., & Zhang, C. (2019). Counterparty credit risk and derivatives pricing. Journal of Financial Economics, 134, 647–668.
Liang, G., & Ren, X. (2007). The credit risk and pricing of OTC options. Asia-Pacific Financial Markets, 14, 45–68.
Liang, G., & Wang, X. (2021). Pricing vulnerable options in a hybrid credit risk model driven by Heston–Nandi GARCH processes. Review of Derivatives Research, 24, 1–30.
Liao, S., & Huang, H. (2005). Pricing Black–Scholes options with correlated interest rate risk and credit risk: An extension. Quantitative Finance, 5, 443–457.
Ma, C., Yue, S., Wu, H., & Ma, Y. (2020). Pricing vulnerable options with stochastic volatility and stochastic interest rate. Computational Economics, 56, 391–429.
Ma, Y., Shrestha, K., & Xu, W. (2017). Pricing vulnerable options with jump clustering. Journal of Futures Markets, 37, 1155–1178.
Pasricha, P., & Goel, A. (2019). Pricing vulnerable power exchange options in an intensity based framework. Journal of Computational and Applied Mathematics, 355, 106–115.
Ritchken, P., & Trevor, R. (1999). Pricing options under generalized GARCH and stochastic volatility processes. Journal of Finance, 54, 377–402.
Tian, L., Wang, G., Wang, X., & Wang, Y. (2014). Pricing vulnerable options with correlated credit risk under jump-diffusion processes. Journal of Futures Markets, 34, 957–979.
Wang, X. (2016). Pricing vulnerable options with stochastic default barriers. Finance Research Letters, 19, 305–313.
Wang, X. (2017). Analytical valuation of vulnerable options in a discrete-time framework. Probability in the Engineering and Informational Sciences, 31, 100–120.
Wang, X. (2018). Pricing vulnerable European options with stochastic correlation. Probability in the Engineering and Informational Sciences, 32, 67–95.
Wang, X. (2021). Analytical valuation of vulnerable European and Asian options in intensity-based models. Journal of Computational and Applied Mathematics, 393, 113412.
Yang, S., Lee, M., & Kim, J. (2014). Pricing vulnerable options under a stochastic volatility model. Applied Mathematics Letters, 34, 7–12.
Acknowledgements
Funding was provided by National Natural Science Foundation of China (Grant No. 11701084).
Author information
Authors and Affiliations
Corresponding author
Additional information
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Appendix
Appendix
Proof of Proposition 2.1
We first derive the closed form of \(f(t;t_i,\phi _1,\phi _2,\phi _3)\) for \(t_i\le t\le T\), that is,
In what follows, the more parsimonious notations f(t), \(A_0(t)\), \(A_1(t)\) and \(A_2(t)\) are used. From the definition of \(f(t;t_i,\phi _1,\phi _2,\phi _3)\), it is obvious that
implying that
According to the law of iterated expectations and the dynamics of the underlying asset and the intensity process, we have that
The expectations in the above expression can be derived using the following fact,
where Z is a standard normal variable. Indeed, we have that
By now, we have obtained the closed forms of \(A_0(t)\), \(A_1(t)\) and \(A_2(t)\) for \(t_i\le t\le T\) as follows,
Now we turn to derive the closed form of \(f(t;t_i,\phi _1,\phi _2,\phi _3)\) for \(0\le t \le t_i\), that is,
Similarly, in the following the more parsimonious notations f(t), \(B_0(t)\), \(B_1(t)\) and \(B_2(t)\) will be used. Actually, we have obtained the expression of \(f(t_i;t_i,\phi _1,\phi _2,\phi _3)\), i.e.,
implying that
Once again, based on the law of iterated expectations and the dynamics of the underlying asset and the intensity process, one gets that
Obviously, the above expectations have similar forms as we have derived before, and hence we have the following results for \(0\le t \le t_i\),
This completes the proof of Proposition 2.1. \(\square \)
Proof of Proposition 2.2
Recall that the prices of fade-in European options without default risk are given by
Rewrite \(F_0\) in the following form,
where
Note that \(f(t;t_i,\phi _1,\phi _2,0)\) is the joint characteristic function of \(\ln S(T)\) and \(\ln S(t_i)\). By inverting the joint characteristic function [see, e.g., Kendall and Stuart (1977)], one gets that
and
Using the change of measure technique [see, e.g., Heston and Nandi (2000), Wang (2018) and Liang and Wang (2021)], one obtains that
and
Therefore, we have obtained the closed form of \(F_0\), i.e.,
In what follows, we turn to derive the closed form of \(FD_0\). We first rewrite it in the following way,
where
Note that \(\pi _{i,5}\)-\(\pi _{i,8}\) have the same form as \(\pi _{i,1}\)-\(\pi _{i,4}\) except for a term \(I(\tau >T)\). As mentioned before, we can deal with this term using the change of measure technique. Hence, we have that
and
It is noted that by replacing \(f(0;t_i,1,0,0)\) and \(f(0;t_i,\cdot ,\cdot ,0)\) with \(f(0;t_i,1,0,-1)\) and \(f(0;t_i,\cdot ,\cdot ,-1)\) we obtain the closed form of \(\pi _{i,5}\) and \(\pi _{i,7}\).
Likewise, we can we can obtain the closed form of \(\pi _{i,6}\) and \(\pi _{i,8}\) given below,
and
This completes the proof of Proposition 2.2. \(\square \)
Rights and permissions
About this article
Cite this article
Wang, X. Valuing fade-in options with default risk in Heston–Nandi GARCH models. Rev Deriv Res 25, 1–22 (2022). https://doi.org/10.1007/s11147-021-09179-3
Accepted:
Published:
Issue Date:
DOI: https://doi.org/10.1007/s11147-021-09179-3