Abstract
This paper studies the cardinality of codes correcting insertions and deletions. We give improved upper and lower bounds on code size. Our upper bound is obtained by utilizing the asymmetric property of list decoding for insertions and deletions and can be seen as analogous to the Elias bound in the Hamming metric. Our non-asymptotic bound is better than the existing bounds when the minimum Levenshtein distance is relatively large. The asymptotic bound exceeds the Elias and the MRRW bounds adapted from the Hamming-metric bounds for the binary and the quaternary cases. Our lower bound improves on the bound by Levenshtein, but its effect is limited and vanishes asymptotically.
Similar content being viewed by others
1 Introduction
We study the existence of codes correcting insertions and deletions. We are interested in deriving upper and lower bounds on the cardinality of codes.
Levenshtein [9] gave asymptotic upper and lower bounds for codes correcting a constant number of insertions and deletions. Later, he presented bounds for correcting any number [11]. Following his work, there have been several studies [3, 7, 8] on the cardinality of codes. However, they mainly focused on codes correcting a constant number of insertions/deletions. Giving better bounds for codes correcting a constant fraction of insertions/deletions has been elusive. See [2] for a recent survey.
In this work, we present upper and lower bounds on the cardinality of codes correcting insertions and deletions. First, we give a non-asymptotic upper bound on the cardinality of codes correcting insertions/deletions. Asymptotically, it implies that for any code \(C \subseteq \Sigma ^n\) of rate R that can correct \(\lfloor \delta n \rfloor - 1\) insertions/deletions, it holds that \(R \le (1 - H_q(\delta ))/(1-\delta )\), where \(|\Sigma | = q\), \(\delta \in [0,1)\), and \(H_q(\cdot )\) is the q-ary entropy function. The bound improves on the asymptotic upper bounds from the literature; The well-known Elias and MRRW bounds for the Hamming metric can also be employed as upper bounds in the Levenshtein metric (insertions and deletions). Our bound improves on them for \(q = 2, 4\).
Our bound is obtained by a similar argument to the Elias bound in the Hamming metric. We use the list size upper bound of [6] for insertions and deletions. It is well-known that any s-deletion correcting code can correct any \(s_1\) insertions and \(s_2\) deletions with \(s_1+s_2=s\). This symmetry in the unique decoding regime does not hold in the list decoding problem. In [6], it is proved that any code with a large Levenshtein distance enables list decoding such that the decoding radius of insertion is superior to that of deletion. We crucially use this property to derive our upper bound.
Next, we give a non-asymptotic lower bound on the cardinality of codes. Our bound improves on the bound by Levenshtein [11] by investigating that every deletion ball contains multiple words that are close to each other in the Levenshtein distance. Asymptotically, our lower bound is the same as in [11].
Finally, we compare our bounds with the existing bounds in the literature. As a non-asymptotic bound, our upper bound is tighter than the bounds in [8, 11] when the minimum distance is relatively large. Our asymptotic upper bound is the best compared with the existing bounds from the Hamming metric for the binary and the quaternary codes. Regarding lower bounds, although our bound strictly improves the bound in [11], its effect is limited and vanishes asymptotically.
1.1 Related work
The existence of positive rate codes correcting a constant fraction of insertions/deletions was presented by Schulman and Zuckerman [14]. Their asymptotic lower bounds were later improved by Levenshtein [11].
Cullina and Kiyavash [3] improved Levenshtein’s upper bound [11] for correcting a constant number of insertions/deletions using a graph-theoretic approach. Kulkarni and Kiyavash [8] derived non-asymptotic upper bounds by a linear programming argument for graph-matching problems. They also gave upper bounds for correcting a constant fraction of insertions/deletions. Although their asymptotic bound (rate function) improved on the bound in [11], it was not given in the closed-form expressions.
For extreme cases where the deletion fraction is either small or high, Guruswami and Wang [5] gave efficient constructions of codes correcting these cases of deletions. For the case that the coding rate is nearly zero, Kash et al. [7] showed a positive-rate binary code correcting the fraction p of insertions/deletions with \(p \ge 0.1737\), which improved on the bound of \(p \ge 0.1334\) in [11]. Bukh, Guruswami, and Haståd [1] significantly improved on the previous results by showing the existence of a positive rate q-ary code with \(p \ge 1 - (2/(q+\sqrt{q}))\), which is \(p \ge 0.4142\) for the binary case. Guruswami, He, and Li [4] showed a slight but highly non-trivial improvement to the upper bound on the fraction of correctable insertions/deletions by codes with a non-zero coding rate. They proved that there is a constant \(\epsilon >0\) such that any q-ary code correcting a \((1 - (1+\epsilon )/q)\)-fraction of insertions/deletions must have a rate approaching 0.
Maringer et al. [12] studied insertion/deletion correcting codes in feedback models and completely determined the maximal asymptotic rate for binary codes.
2 Code size upper bound
Let \(\Sigma \) be a finite alphabet. The Levenshtein distance \({d}_\textrm{L}(x, y)\) between two words x and y is the minimum number of symbol insertions and deletions needed to transform x into y. For a code \(C \subseteq \Sigma ^n\), its minimum Levenshtein distance is the minimum distance \({d}_\textrm{L}(c_1, c_2)\) of every pair of distinct codewords \(c_1, c_2 \in C\). Since any two codewords in C are of the same length, the minimum Levenshtein distance of C takes an even number. It is well-known that a code with minimum Levenshtein distance d can correct any \(s_1\) insertions and \(s_2\) deletions as long as \(s_1 + s_2 \le d/2 - 1\). The Levenshtein distance between two words in \(\Sigma ^n\) takes integer values from 0 to 2n. Thus, we consider the normalized Levenshtein distance \(\delta = d/2n\) in the analysis. The value \(\delta \in [0,1]\) also represents the fraction of insertions/deletions that can be corrected since we require \((s_1+s_2)/n \le (d/2 - 1)/n = \delta - 1/n\), which is asymptotically equal to \(\delta \).
Let \(C \subseteq \Sigma ^n\) be a code of minimum Levenshtein distance d with \(|\Sigma |=q\). For a word \(x \in \Sigma ^n\), let \(I_t(x) \subseteq \Sigma ^{n+t}\) be the set of its supersequences of length \(n+t\). Namely, \(I_t(x)\) consists of words obtained from x by inserting t symbols. Similarly, let \(D_t(x)\) be the set of words obtained from x by deleting t symbols. It is known [10] that the size of \(I_t(x)\) does not depend on x and
First, we give a simple sphere packing bound. We use the fact that the number of supersequences, \(|I_t(x)|\), is independent of x.
Theorem 1
Let \(C \subseteq \Sigma ^n\) be a code of minimum Levenshtein distance d and \(|\Sigma |=q\). It holds that
Proof
For each codeword \(c \in C\), consider the set of supersequences \(I_{d/2-1}(c) \subseteq \Sigma ^{n+d/2-1}\). Since the code has minimum Levenshtein distance d, each \(I_{d/2-1}(c)\) should be disjoint. Thus,
The statement follows by the equality \(|I_{d/2-1}(c)| = I_q(n, d/2-1)\) for any \(c \in C\). \(\square \)
Next, we prove our main theorem, which can be seen as an Elias-type upper bound on the code size in the Levenshtein metric.
Theorem 2
Let \(C \subseteq \Sigma ^n\) be a code of minimum Levenshtein distance \(d < 2n\) and \(|\Sigma |=q\). For any integer \(t \ge 0\) with
it holds that
Proof
By double counting, the sum of the cardinalities of \(I_t(x)\) of all \(x \in \Sigma ^n\) is equal to the sum of the cardinalities of \(D_t(y)\) of all \(y \in \Sigma ^{n+t}\).
Namely,
By considering the intersection with C,
Thus, by choosing \(y \in \Sigma ^{n+t}\) uniformly at random,
The averaging argument implies that there exists \(y \in \Sigma ^{n+t}\) such that
We have the following lemma.
Lemma 1
For any non-negative integer t with \(t < nd/(2n-d)\) and \(y \in \Sigma ^{n+t}\), it holds that
Proof
In [6], \(B_\textsf{L}(v, t_\textsf{I}, t_\textsf{D})\) is defined as the set of words that can be obtained from v by at most \(t_\textsf{I}\) insertions and at most \(t_\textsf{D}\) deletions. Then, for \(C \subseteq \Sigma ^n\) and \(y \in \Sigma ^{n+t}\), we can see that \(B_\textsf{L}(y, 0, t) \cap C = D_t(y) \cap C\). Lemma 1 of [6] with \(t_\textsf{I}=t\) and \(t_\textsf{D}=0\) implies that if \(d/2 > t n/(n+t)\), \(|D_t(y) \cap C| \le (n+t)(d/2)/((n+t)d/2 - tn)\) for every \(y \in \Sigma ^{n+t}\), which implies the statement. \(\square \)
By combining (5) and Lemma 1, the statement follows. \(\square \)
We analyze asymptotics of Theorems 1 and 2. For a code \(C \subseteq \Sigma ^n\) of distance d, let \(\delta = d/2n\) and \(\gamma = t/n\) for \(t \ge 0\). Let \(A_q(n,d)\) be the maximum size of code \(C \subseteq \Sigma ^n\) of minimum Levenshtein distance d, where \(|\Sigma | = q\). For \(\delta \in [0,1]\), let
be the asymptotic coding rate achievable for normalized Levenshtein distance \(\delta \). Note that \(R_q(\delta ) = 0\) for \(\delta \ge 1-q^{-1}\) (See, for example, [1, Section 1]).
Let \(\textrm{Vol}_q(n, \ell )\) be the volume of the Hamming ball of radius \(\ell \) in \(\mathbb {F}_q^n\). Namely, \(\textrm{Vol}_q(n,\ell ) = \sum _{i=0}^\ell \left( {\begin{array}{c}n\\ i\end{array}}\right) (q-1)^i\). It is well-known (cf. [13, Lemma 4.8]) that, for \(0 \le \ell \le n\),
where \(H_q(x) = -x \log _qx - (1-x)\log _q(1-x)+x\log _q(q-1)\). Since \(I_q(n, t) = \textrm{Vol}_q(n+t, t)\),
Regarding Theorem 1, it holds that
By Theorem 1, the rate R of C is bounded above by
Thus, we have the following corollary.
Corollary 1
Regarding Theorem 2, condition (2) can be rewritten as
Let \(\gamma = \delta /(1-\delta ) - 1/n\). The bound (3) can be rewritten as
Since
the rate R of C is bounded above by
We obtain the following corollary.
Corollary 2
2.1 Bounds from Hamming-metric bounds
For a code \(C \subseteq \Sigma ^n\), let \(d_h\) be the minimum Hamming distance of C. It is well-known that the minimum Levenshtein distance d of C satisfies \(d \le 2d_h\). Thus, whenever we have an upper bound for a code of minimum Hamming distance \(d_h\), we can use the same bound for a code of minimum Levenshtein distance \(d_h/2\). More specifically, if a code \(C \subseteq \Sigma ^n\) satisfies \(|C| \le f(q,n,d_h)\), then \(|C| \le f(q,n, d/2)\) as long as f is a monotonically decreasing function on the third argument. Let \(\delta = d/2n\) and \(\delta _h = d_h/n\). Similarly, if we have a bound on the coding rate \(R \le g(q,\delta _h)\), then we have \(R_q(\delta ) \le g(q,\delta )\) if g is monotonically decreasing on the second argument.
As far as we know, the best-known upper bounds for coding rate with respect to normalized minimum Levenshtein distance are obtained by the bounds for Hamming metric. The following bounds are well-known in the literature.
Theorem 3
For \(0 \le \delta < \theta = 1 - q^{-1}\),
3 Code size lower bounds
Next, we consider lower bounds on \(A_q(n,d)\) for codes \(C \subseteq \Sigma ^n\) with \(|\Sigma |=q\). We assume that d is even. For \(x \in \Sigma ^n\) and non-negative integers t, s with \(t \le n\), let \(L_{t, s}(x)\) be the set of words that can be obtained from x by deleting t symbols and inserting s symbols. By definition, it holds that \(L_{t,0}(x) = D_t(x)\) and \(L_{0,s}(x) = I_s(x)\).
We would like to derive an upper bound on the average size of \(L_{t, t}(x)\) for \(x \in \Sigma ^n\) and \(t \le n\). This is because it gives a lower bound on \(A_{q}(n,d)\) as discussed in [11, 15]. More specifically, for any \(X \subseteq \Sigma ^n\), let
be the average size of \(L_{t,t}(x)\) in X. Then, there exists a code \(C \subseteq \Sigma ^n\) of minimum Levenshtein distance d satisfying
For \(x = (x_1, \dots , x_n) \in \Sigma ^n\) and \(i \in [1, n-1]\), we say \((x_i,x_{i+1})\) is a distinct adjacent pair if \(x_i \ne x_{i+1}\). Let \(IP(x) = \{ (i, {i+1}): x_i \ne x_{i+1} \}\) be the index-pair set of distinct adjacent pairs in x. We say \(P \subseteq IP(x)\) is disjoint if \(P = \{({i_1},{i_1+1}), \dots , ({i_p}, {i_p+1})\}\) satisfies \(i_j+1 \ne i_\ell \) for every distinct \(j, \ell \in \{1, \dots , p\}\). We denote by p(x) the maximum size of disjoint index-pair sets of distinct adjacent pairs in x. For example, for \(x = 01101\), we have \(IP(x) = \{ (1,2), (3,4), (4,5)\}\). The sets \(\{(1,2), (3,4)\}\) and \(\{(1,2), (4,5)\}\) are disjoint, but \(\{(3,4),(4,5)\}\) is not. We have \(p(01101) = 2\). For consistency, we consider the leftmost maximum-sized disjoint index-pair set in x. In the case that \(x = 01101\), the leftmost one is \(\{(1,2), (3,4)\}\). Similarly, for \(y = 010100\) and \(y' = 010111\), the (leftmost) maximum-sized disjoint index-pair set is \(\{ (1,2), (3,4)\}\), and hence \(p(y) = p(y') = 2\).
We observe that for any positive integer \(p' \le p(x)\) satisfying \(p' \le \min \{t, n-t\}\), there are \(2^{p'}\) words in \(D_t(x)\) such that they are within a Levenshtein distance of \(2p'\) from each other. The reason is as follows. Since \(p' \le p(x)\), there are \(n - 2p'\) indices in \(\{1, \dots , n\}\) such that they are not contained in a disjoint index-pair set of distinct adjacent pairs in x. First, we delete \(t - p'\) symbols from x out of the \(n - 2p'\) indices. This procedure requires that \(p' \le \min \{t,n-t\}\). Let \(y \in \Sigma ^{n-t+p'}\) be the resulting word. Second, we delete one of the two symbols in \(p'\) distinct adjacent pairs from y. There are \(2^{p'}\) possible deletion patterns, resulting in all different words of length \(n-t\). Since each resulting word and y have Levenshtein distance \(p'\), the \(2^{p'}\) words are within a Levenshtein distance of \(2p'\). In other words, \(D_t(x)\) contains \(2^{p'}\) words \(\{z_1, \dots , z_{2^{p'}}\}\) such that all are subsequences of \(y \in \Sigma ^{n - t + p'}\). We have
Let \(Z = \{z_1, \dots , z_{2^{p'}}\}\). For any integer \(p' \le p(x)\) with \(p' \le \min \{t,n-t\}\), it holds that
Note that \(p'\) should satisfy \(p' \le \min \{ p(x), t, n-t\}\). Since \(x \in \Sigma ^n\) may have \(p(x) = 0\), it is impossible to choose \(p' > 0\) such that \(p' \le p(x)\) for every \(x \in \Sigma ^n\). Thus, we consider a subset \(X \subseteq \Sigma ^n\) and its partition \(X = X_0 \cup X_1\) such that \(X_1 = \{ x \in X: p(x) \ge p' \}\) for some \(p' \in [0, \min \{t,n-t\}]\) with \(p' > 0\). Then, as an upper bound on \(|L_{t,t}(x)|\), we can use \(L^*_{t,p'}(x)\) for \(x \in X_1\) and \(|D_t(x)|\cdot I_q(n-t,t)\) for \(x \in X_0\).
For integers n and \(p \in [0, n/2 ]\), let \(N_{n,q}(p)\) be the number of words \(x \in \Sigma ^n\) such that \(p(x) = p\), where \(|\Sigma | = q\). The value of \(N_{n,q}(p)\) is given by Theorem 4 below. When \(X_1\) is given by \(\{ x \in \Sigma ^n: p(x) \ge p' \}\), it holds that \(|X_1| = \sum _{p=p'}^{\lfloor n/2 \rfloor } N_{n,q}(p)\).
For a partition \(X = X_0 \cup X_1\) with \(X_1 = \{ x \in \Sigma ^n: p(x) \ge p' \}\), we have that
We use (8) for our lower bound of Theorem 5.
We determine \(N_{n,q}(p)\) for \(p \in [0, n/2]\).
Theorem 4
For integers \(n > 0\), \(p \in [0, n/2]\), and \(q \ge 2\),
Proof
We count the number of words \(x \in \Sigma ^n\) such that \(p(x) = p\). When \(p(x) = 0\), x should be a repetition of the same symbol in \(\Sigma \). Thus, \(N_{n,q}(0) = q\). Hereafter, we assume \(p > 0\). Let \((i_1, i_1+1), \dots , (i_p, i_p+1) \in \{1, \dots , n\}^2\) be p index-pairs of distinct adjacent pairs such that \(i_1 \le \cdots \le i_p\). Let \((a_1, a_1'), \dots , (a_p, a_p') \in \Sigma ^2\) be the corresponding distinct adjacent pairs, where their concrete values are yet determined. Since the order of p pairs \((a_i, a_i')\) is fixed, we can construct all words x with \(p(x) = p\) by inserting \(n-2p\) symbols into the word \(a_1a_1'a_2a_2'\cdots a_pa_p'\). There are \(p+1\) possible places to which symbols can be inserted. Namely, the resulting word should be of the form \(w_1 a_1a_1' w_2 a_2a_2' w_3 \cdots w_p a_pa_p'w_{p+1}\), where \(w_i \in \Sigma ^*\). Here, we consider the leftmost maximum-sized disjoint index-pair set in x. By the property of distinct adjacent pairs, \(w_1\) must be the empty string or repetition of \(a_1\). Similarly, for \(i \in \{ 2, \dots , p\}\), \(w_i\) must be the empty string or repetition of \(a_i\). Since we consider the leftmost disjoint index-pairs, different from the previous cases, \(w_{p+1}\) can be the empty string or repetition of any fixed symbol in \(\Sigma \).
First, suppose that \(w_{p+1}\) is the empty string. Then the number of words x with \(p(x) = p\) is determined by the number of possible lengths of \(w_1, \dots , w_p\) and possible combinations \((a_i,a_i')\). Since the rightmost symbols are fixed to be \(a_pa_p'\), the number of possible lengths is equal to the the number of ways of selecting \(p-1\) items from \(n - 2p + (p-1)\) items, which is \(\left( {\begin{array}{c}n - p-1\\ p-1\end{array}}\right) \). There are \(q(q-1)\) combinations for each \((a_i, a_i')\). Hence, the number \(N_{n,q}(p)\) when \(|w_{p+1}|= 0\) is equal to \(q^p(q-1)^p \left( {\begin{array}{c}n-p-1\\ p-1\end{array}}\right) \). Second, consider the case that \(|w_{p+1}| > 0\). In this case, we count the number of possible lengths of \(w_1, \dots , w_p, w_{p+1}\) and possible combinations \((a_i,a_i')\). Since \(|w_{p+1}| > 0\), we can assume that one symbol (length) has been assigned to \(w_{p+1}\). Then, the number of possible lengths is equal to the number of ways of selecting p items from \(n - 2p - 1 + p\) items, which is \(\left( {\begin{array}{c}n- p -1\\ p\end{array}}\right) \). As in the previous case, the number of combinations for \((a_i, a_i')\)’s are \((q(q-1))^p\), and there are q possible symbols corresponding to \(w_{p+1}\). Thus, the number \(N_{n,q}(p)\) when \(|w_{p+1}| > 0\) is \(q^{p+1}(q-1)^p \left( {\begin{array}{c}n-p-1\\ p\end{array}}\right) \).
Therefore, for \(p \ge 1\), we have
When \(p=0\), the above gives \(N_{n,q}(0) = q\). Hence, the statement follows. \(\square \)
By using (7) and (8), we have the following theorem.
Theorem 5
For a set \(X \subseteq \Sigma ^n\) and its partition \(X = X_0 \cup X_1\) such that \(X_1 = \{ x \in \Sigma ^n: p(x) \ge p' \}\) for some \(p' \in [0, \min \{t,n-t\}]\), it holds that
where \(t = d/2 - 1\).
We give an explicit expression by choosing \(X = \Sigma ^n\) and \(p'=1\),
Corollary 3
where \(t = d/2 - 1 > 0\).
Proof
When \(X = \Sigma ^n\), it follows from (4) that \(\sum _{x \in X} |D_t(x)| \cdot I_q(n-t,t) = q^{n-t} \cdot I_q(n-t,t)^2\). By choose \(p'=1\), since \(N_{n,q}(0)=q\) and \(\sum _{p=0}^{\lfloor n/2 \rfloor }N_{n,q}(p) = q^n\), we have
By combining the above and Theorem 5, the statement follows. \(\square \)
Since Levenshtein [11] gave a lower bound of \(A_q(n,d) \ge q^n/(q^{-t}\cdot I_q(n-t,t)^2)\) for \(t = d/2-1\), Corollary 3 improves his lower bound. Its effect, however, vanishes when d becomes large; Thus, the asymptotic lower bound on the coding rate given by Corollary 3 is the same as [11].
4 Comparison
First, we compare code-size upper bounds given by [8, 11] and Theorems 1 and 2. Table 1 displays numerical values for several parameters q, n, and d. Specifically, we use the bounds in [11, Theorem 2], where we take the minimum over parameter r, and [8, Corollary 4.2]. Though the non-asymptotic bound of [8] achieves the best when d is small such as 4 and 10, Theorem 2 is much better when d is relatively large.
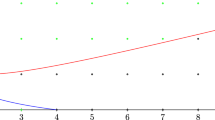
Next, we investigate asymptotic behaviors. Figures 1 and 2 show asymptotic bounds on the rate function \(R_q(\delta )\) for \(q=2\) and \(q=4\), respectively. Corollary 2 gives the best upper bounds in both cases. For larger q, Corollary 2 is inferior to the MRRW bound, especially for large \(\delta \). Regarding lower bounds, [11] gave a bound (displayed as Levenshtein02), and [1] showed that there exist q-ary codes of rate R that achieve \(\delta \ge 1 - (2/(q+ \sqrt{q}))\) for sufficiently small \(R >0\) (displayed as BGH17). Also, it is proved in [4] that there is a small constant \(\epsilon >0\) such that \(R = 0\) for \(\delta \ge 1 - (1+\epsilon )/q\) (omitted in the figures). The asymptotic upper bounds of [8, 11] were not given in the closed form. Hence it is not easy to make a clear comparison. By comparing with the plotted bound of [8, Fig. 1], we can see that Corollary 2 gives tighter bounds on \(\delta \ge 0.1\) for \(q=2\) and \(\delta \ge 0.2\) for \(q=4\).
Table 2 shows the numerical values of the lower bounds of [11, Theorem 1] and Corollary 3. As we can see, the improvement by Corollary 3 is small.
5 Conclusions
This paper has presented improved upper and lower bounds on code size for correcting insertions and deletions. In particular, our upper bound improves the existing bounds in both non-asymptotic and asymptotic senses. An interesting future work is to develop an upper bound superior to the MRRW bound for large alphabet size q and relative distance \(\delta \). Our bound is inferior in some range for \(q \ge 5\). A key lemma may be a list-size upper bound of insertions/deletion (as Lemma 1) employing q explicitly in the bound.
References
Bukh B., Guruswami V., Håstad J.: An improved bound on the fraction of correctable deletions. IEEE Trans. Inf. Theory 63(1), 93–103 (2017).
Cheraghchi M., Ribeiro J.L.: An overview of capacity results for synchronization channels. IEEE Trans. Inf. Theory 67(6), 3207–3232 (2021).
Cullina D., Kiyavash N.: An improvement to Levenshtein’s upper bound on the cardinality of deletion correcting codes. IEEE Trans. Inf. Theory 60(7), 3862–3870 (2014).
Guruswami, V., He, X., Li, R.: The zero-rate threshold for adversarial bit-deletions is less than 1/2. In: 62nd IEEE Annual Symposium on Foundations of Computer Science, FOCS 2021, Denver, CO, USA, February 7–10, 2022, pp. 727–738. IEEE (2021)
Guruswami V., Wang C.: Deletion codes in the high-noise and high-rate regimes. IEEE Trans. Inf. Theory 63(4), 1961–1970 (2017).
Hayashi T., Yasunaga K.: On the list decodability of insertions and deletions. IEEE Trans. Inf. Theory 66(9), 5335–5343 (2020).
Kash, I.A., Mitzenmacher, M., Thaler, J., Ullman, J.R.: On the zero-error capacity threshold for deletion channels. In: Information Theory and Applications Workshop, ITA 2011, San Diego, California, USA, February 6–11, 2011, pp. 285–289. IEEE (2011).
Kulkarni A.A., Kiyavash N.: Nonasymptotic upper bounds for deletion correcting codes. IEEE Trans. Inf. Theory 59(8), 5115–5130 (2013).
Levenshtein V.I.: Binary codes capable of correcting deletions, insertions, and reversals. Soviet Physics Doklady 10(8), 707–710 (1966).
Levenshtein V.I.: Efficient reconstruction of sequences from their subsequences or supersequences. J. Comb. Theory Ser. A 93(2), 310–332 (2001).
Levenshtein, V.I.: Bounds for deletion/insertion correcting codes. In: Proceedings IEEE International Symposium on Information Theory, p. 370 (2002).
Maringer G., Polyanskii N.A., Vorobyev I.V., Welter L.: Feedback insertion-deletion codes. Probl. Inf. Transm. 57(3), 212–240 (2021).
Roth R.M.: Introduction to Coding Theory. Cambridge University Press, Cambridge (2006).
Schulman L.J., Zuckerman D.: Asymptotically good codes correcting insertions, deletions, and transpositions. IEEE Trans. Inf. Theory 45(7), 2552–2557 (1999).
Tolhuizen L.M.G.M.: The generalized Gilbert-Varshamov bound is implied by Turan’s theorem. IEEE Trans. Inf. Theory 43(5), 1605–1606 (1997).
Acknowledgements
This work was supported in part by JSPS Grants-in-Aid for Scientific Research Number 18K11159.
Author information
Authors and Affiliations
Corresponding author
Additional information
Communicated by C. J. Colbourn.
Publisher's Note
Springer Nature remains neutral with regard to jurisdictional claims in published maps and institutional affiliations.
Rights and permissions
Open Access This article is licensed under a Creative Commons Attribution 4.0 International License, which permits use, sharing, adaptation, distribution and reproduction in any medium or format, as long as you give appropriate credit to the original author(s) and the source, provide a link to the Creative Commons licence, and indicate if changes were made. The images or other third party material in this article are included in the article’s Creative Commons licence, unless indicated otherwise in a credit line to the material. If material is not included in the article’s Creative Commons licence and your intended use is not permitted by statutory regulation or exceeds the permitted use, you will need to obtain permission directly from the copyright holder. To view a copy of this licence, visit http://creativecommons.org/licenses/by/4.0/.
About this article
Cite this article
Yasunaga, K. Improved bounds for codes correcting insertions and deletions. Des. Codes Cryptogr. (2024). https://doi.org/10.1007/s10623-023-01342-1
Received:
Revised:
Accepted:
Published:
DOI: https://doi.org/10.1007/s10623-023-01342-1